Google Issues New Warning About the Quantum Computing Security Apocalypse
I’m just the blogger who works nights and weekends for Gizmodo. If I could get into the nitty-gritty of cryptography and quantum computing, I would be off doing that. With that said, this concerns a somewhat ominous security-related update from Google that happens to involve cryptography and quantum computing.
On Wednesday, Google moved the date by which it thinks the security community should prepare for Q-Day to 2029. What’s Q-Day? Glad you asked. It’s the theoretical future day when a quantum computer will have the capability to essentially break all cryptographic security, potentially creating a sort of hacking and identity theft armageddon.
These preparations are known as the transition to post-quantum cryptography or PQC.
Moving the deadline for the switch to PQC to 2029—around the time of the next U.S. presidential inauguration—is a pretty dramatic escalation. It sounds like the previously accepted timeline was not a tangible date in the future, but a sort of hand wave, like the “day” in the future when there’s abundant energy from nuclear fusion. Pure speculation, or is it?
Now it sounds like a) Google is acting out of an abundance of caution, and b) something has changed.
What’s changed, according to Ars Technica’s Dan Goodin may have something to do with Google’s report last year showing, as Goodin put it “that a 2048-bit RSA integer could be factored in less than a week with a quantum computer with 1 million ‘noisy qubits.’”
Like I said, I’m just some guy, but what little I’ve read about quantum computing, especially a much deeper dive into this topic from my colleague Gayoung Lee, tells me that this “noisy” part is critical.
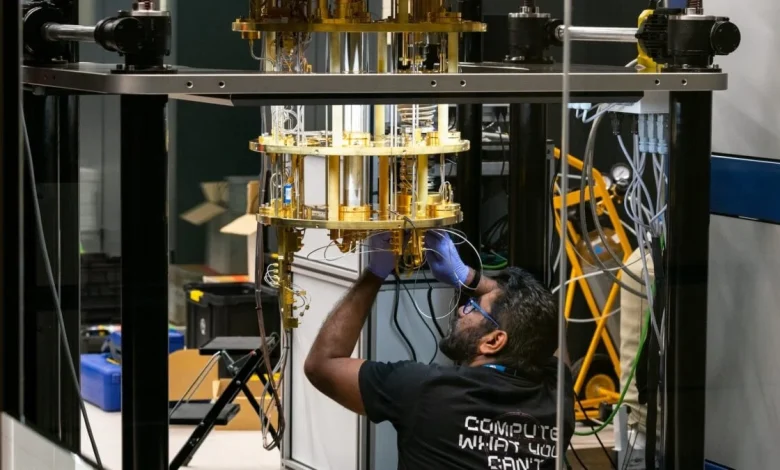
Current quantum computers, I’m led to believe, are basically Playskool quantum computers. They may have actual “qubits,” and those qubits may actually enter “superpositions” and undergo “entanglement” (I’m truly out at the edge of my understanding here). But they are too error-prone to be any sort of revolution in computing, or threat. The qubits are too noisy—which is why they call them Noisy Intermediate Scale Quantum (NISQ) computers.
So to quote Goodin again, “In 2012, most estimates were that a 2048-bit RSA key could be broken by a quantum computer with a billion physical qubits.” One million noisy qubits is apparently a much more doable prospect than a billion precise ones, thus Google’s sense of alarm.
Does this mean you need to get in your apocalypse bunker, or ask your smartest cousin to set up some kind of PQC action plan for all your gadgets? (Q-Day is sometimes compared to the Y2K bug) Doubtful. It sounds like this is mainly something in the realm of cybersecurity that cryptographers need to stay on top of.
But it also sounds like are remarkable change in our expectations for quantum computing. Capabilities once thought further out—unfortunately the potentially evil capabilities—may be here before the arrival of the pristine and flawless quantum computers computer scientists were imagining.